Technology May 20, 2026
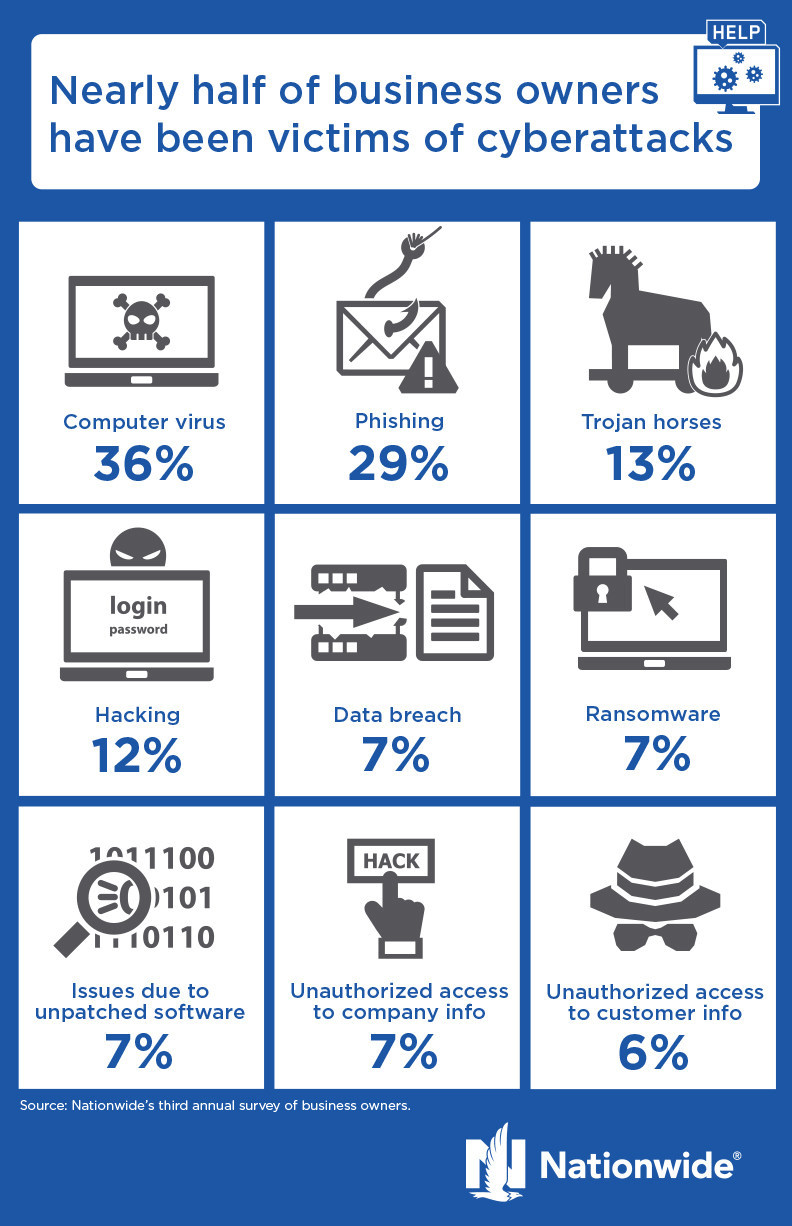
Verito and NATP Partner on AI Governance and Cybersecurity Curriculum for Tax Professionals
Verito is partnering with the National Association of Tax Professionals to deliver an AI governance and cybersecurity curriculum, built specifically for tax preparers, to NATP's 23,000-plus members nationwide.